איומים מתמשכים ומתקדמים (APT) פועלים באופן שונה ממתקפות סייבר רגילות. במקום קמפיינים נרחבים, הם מסתמכים על מיקוד מדויק, פיתיונות מתוכננים בקפידה ותוכנות זדוניות שנועדו להשתלב בתהליכי העבודה השוטפים. התוקפים מרבים להשתמש במסמכים כנשק, להסתיר מטענים זדוניים בתוך כלים לגיטימיים, ולתכנן מתקפות באופן ספציפי כדי לעקוף מערכות הגנה מסורתיות המבוססות על חתימות.
כדי להדגים כיצד ניתן עדיין לחשוף איומים אלה, ניתחנו חמש דוגמאות אמיתיות של מתקפות APT שכוונו לסביבות ממשלתיות, ביטחוניות, פיננסיות ותעשייתיות במזרח התיכון, באיראן, בפקיסטן ובדרום אסיה. בכל אחד מהמקרים, MetaDefender זיהתה וניתחה את המתקפות באמצעות מערך הזיהוי המאוחד שלה לאיומים מסוג "יום אפס", המשלב דירוג מוניטין של איומים, סביבת בדיקה אדפטיבית (sandboxing), דירוג איומים וחיפוש דמיון באמצעות למידת מכונה.
מדוע מתקפות APT ממוקדות הן בעלות חשיבות
קמפיינים ממוקדים מסוג APT נועדו לחדור לארגונים ספציפיים ולא להתפשט בקנה מידה נרחב. מתקפות סייבר אלה מתמקדות לרוב בגופים ממשלתיים, בתשתיות קריטיות, במוסדות פיננסיים ובמגזרים תעשייתיים שבהם למידע גנוב או לשיבוש פעילות יש ערך אסטרטגי.
בניגוד לתוכנות זדוניות נפוצות, מתקפות APT מתוכננות בקפידה כדי לעקוף את אמצעי ההגנה המסורתיים. התוקפים מסתמכים לעתים קרובות על מסמכי פישינג ממוקד, העברת מטען זדוני בשלבים וטכניקות שנועדו לעקוף מערכות זיהוי מבוססות חתימות או מערכות ניתוח אוטומטיות.
ההתוחכמות הגוברת הזו היא אחת הסיבות שבגללן ארגונים מעניקים עדיפות לבדיקות התנהגותיות ולזיהוי איומים מסוג "יום אפס". צוותי האבטחה זקוקים יותר ויותר ליכולת לראות כיצד קבצים מתנהגים במהלך ההפעלה, ולא רק כיצד הם נראים בבדיקה סטטית, כדי לחשוף איומים שתוכננו במכוון להישאר מוסתרים.
חמש דוגמאות אמיתיות למתקפות APT
מתקפה מס' 1: קמפיין פישינג ממוקד המכוון לארגונים ממשלתיים
הקשר
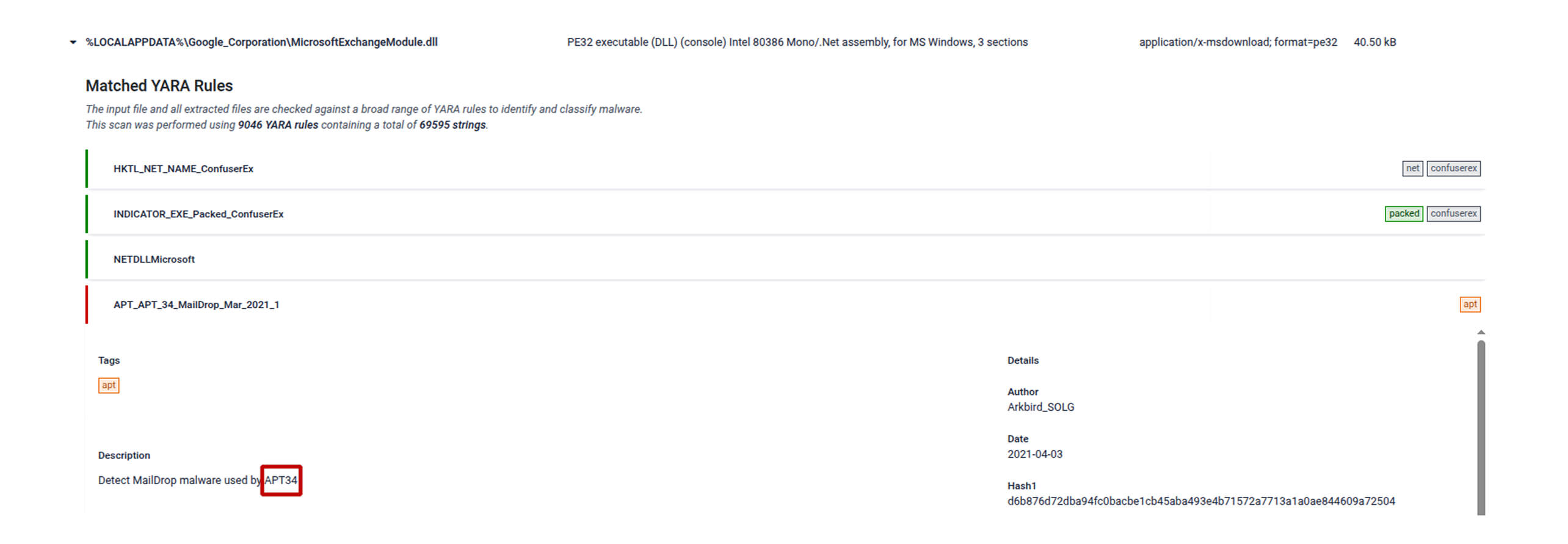
APT34, הידועה גם בשם OilRig, היא קבוצת תקיפה החשודה כקשורה לממשל האיראני, הפועלת כבר למעלה מעשור. הקבוצה ידועה במבצעי ריגול סייבר ממוקדים נגד ארגונים ממשלתיים, אנרגיה ופיננסיים ברחבי המזרח התיכון, והיא נוהגת להסתמך לעתים קרובות על הודעות דוא"ל מסוג "ספיר-פישינג" (spear-phishing) המתוכננות בקפידה כדי להשיג גישה ראשונית.
מדו"חות מודיעין איומים עולה כי APT34 נוהגת להשתמש במסמכים זדוניים כדי להפיץ תוכנות זדוניות מותאמות אישית ולשמור על גישה ארוכת טווח לסביבות הקורבנות. קמפיינים אלה מתוכננים כך שייראו שגרתיים בעיני הנמען, תוך פריסה שקטה של כלים למעקב ולאיסוף נתונים.
סקירת ההתקפה
במקרה זה, התוקפים הפיצו מסמך Microsoft Word זדוני באמצעות דוא"ל פישינג ממוקד, שכוון לארגונים ממשלתיים וימיים. שם הקובץ היה בערבית, והוא עסק בנושא מוכנות כלי שיט ימיים, מה שמרמז כי הוא נוצר כך שייראה רלוונטי לנמענים צבאיים או דיפלומטיים באזור.
עם פתיחתו, המסמך ביקש מהמשתמש להפעיל את המאקרו. לאחר ההפעלה, המאקרו יצר ספרייה שהוסוותה כתיקייה לגיטימית הקשורה ל-Google והטמיע קבצים נוספים במערכת. לאחר מכן, המאקרו ביצע סקריפט VBA קצר שהשתמש ב-PowerShell וב-NET Reflection כדי לטעון שני קבצי DLL המהווים מטען זדוני השייכים למשפחת תוכנות הזדוניות Karkoff.
אזהרה לתעשייה
מתקפה זו מדגישה את המשך השימוש בהתקפות פישינג ממוקדות המבוססות על מסמכים כדי לחדור לסביבות רגישות. גופים ממשלתיים, ארגונים דיפלומטיים וגופים ימיים נותרים יעדים נפוצים, שכן המידע שברשותם עשוי להוות נכס מודיעיני אסטרטגי.
צוותי האבטחה במגזרים אלה צריכים להתייחס לאיומים המבוססים על מסמכים כאל נתיב פריצה עיקרי. אפילו קובץ זדוני אחד שנשלח בדוא"ל עלול לשמש כנקודת כניסה למבצע ריגול נרחב יותר.
למידע נוסף על מתקפה זו ולצפייה בניתוח המלא, בקרו בדו"חOPSWAT .
התקפה מס' 2: קמפיין פישינג ממוקד באמצעות מאקרו מוגנים
הקשר
APT-C-35, הידועה בכינויה "Donot", היא קבוצת תקיפה ותיקה הידועה בקמפיינים ממוקדים של פישינג ממוקד (spear-phishing) נגד גופים ממשלתיים וארגונים אסטרטגיים. חוקרי אבטחה הבחינו כי הקבוצה משתמשת בפיתיונות מבוססי מסמכים ובמסגרות תוכנות זדוניות מותאמות אישית כדי לחדור למערכות של קורבנות ספציפיים, במקום לבצע מתקפות בקנה מידה נרחב.
דיווחים אחרונים מדגישים גם את המשך פיתוח כלי העבודה של הקבוצה, לרבות שיפורים במסגרת Jaca, התומכת בפעילויות ריגול ואיסוף נתונים. קמפיינים אלה ממחישים כיצד הקבוצה מתאימה את הטכניקות שלה כדי לחמוק מניתוח אוטומטי ולשמור על גישה בתוך הסביבות המותקפות.
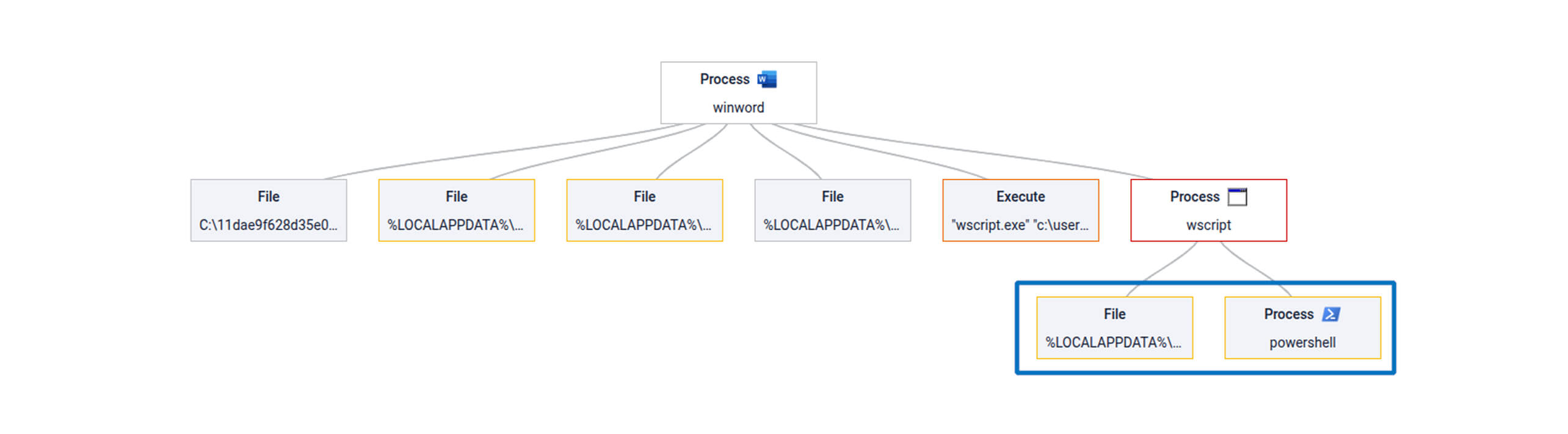
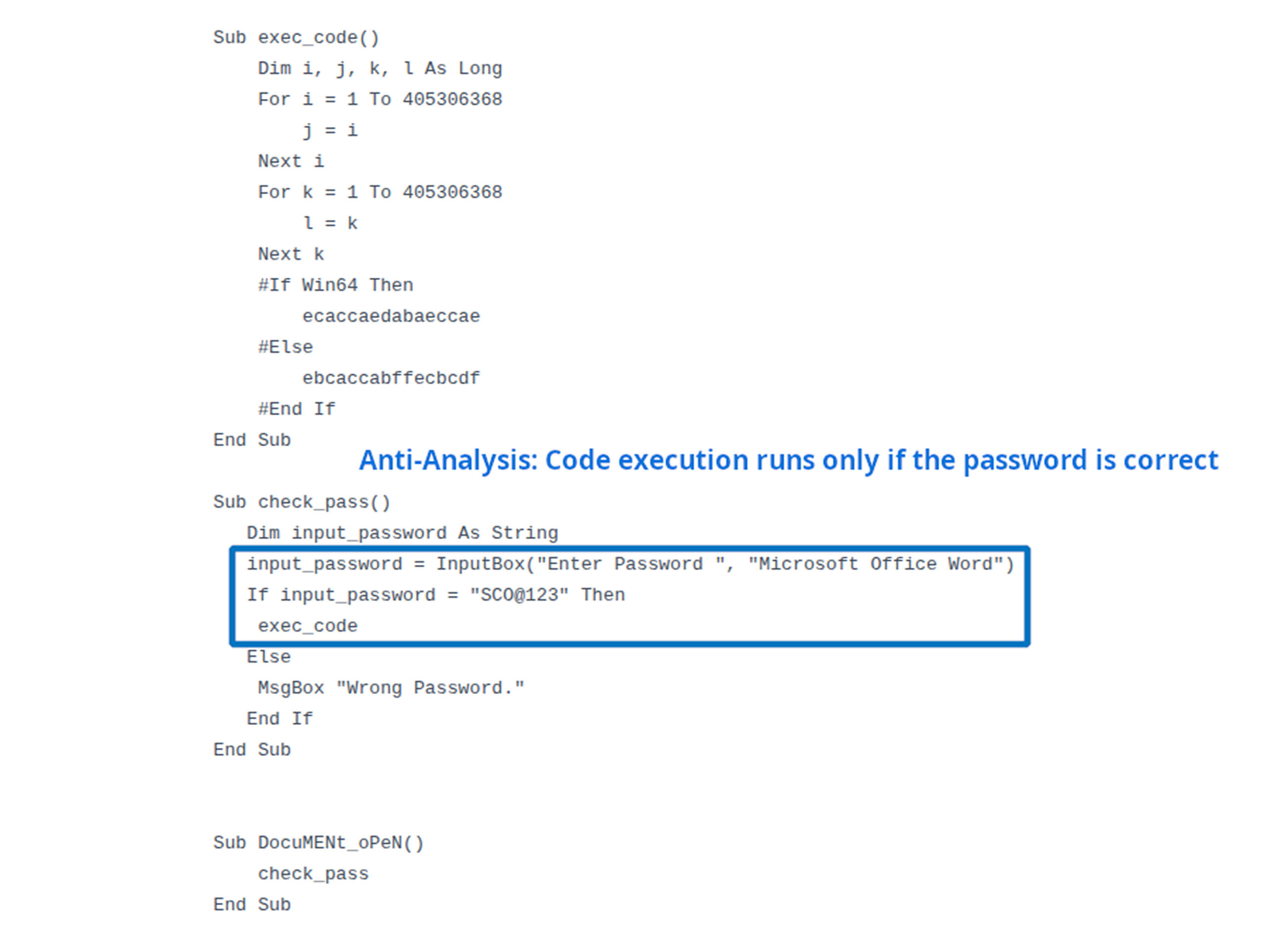
סקירת ההתקפה
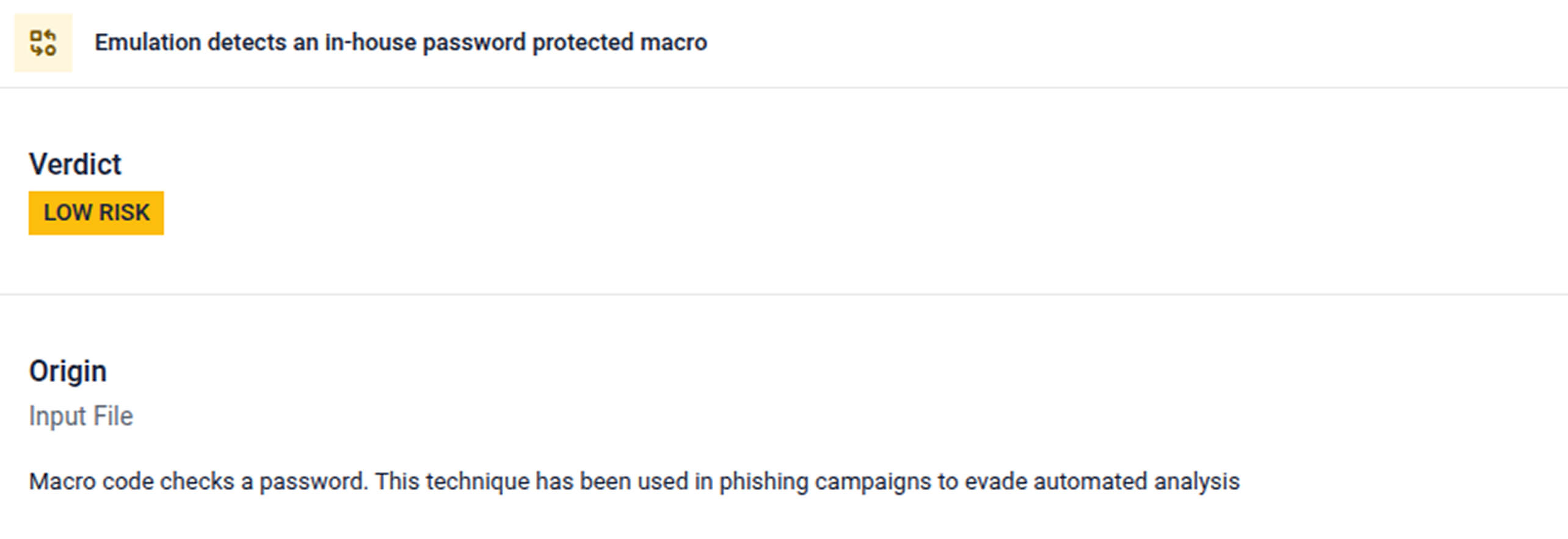
בדוגמה זו, התוקפים הפיצו מסמך Microsoft Office זדוני באמצעות דוא"ל פישינג ממוקד, שכוון לארגונים הקשורים לתחומי הייצור והממשל בדרום אסיה. המסמך הכיל מאקרו המוגן בסיסמה, כאשר הסיסמה הנכונה צורפה לנוחות הקורבן בהודעת הדוא"ל, במטרה לעודד אותו לאפשר את הפעלתו.
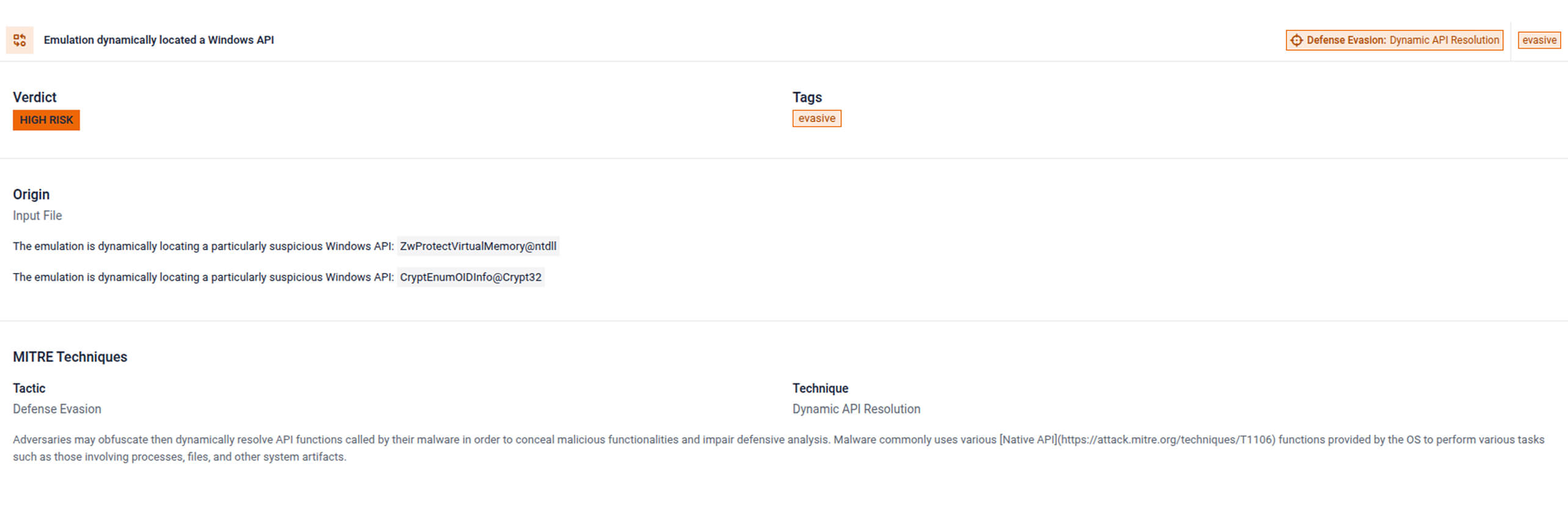
לאחר הזנת הסיסמה הנכונה, המאקרו ביצע לוגיקה זדונית מוסתרת שנועדה לעקוף ניתוח אוטומטי. הקוד כלל לולאות חסרות משמעות שנועדו לבזבז משאבי ניתוח, קוד מעטפת שנוצר באופן דינמי, ובסופו של דבר ביצע את המטען באמצעות מנגנון API CryptEnumOIDInfo של Windows, מה שאפשר לתקיפה לעקוף טכניקות זיהוי מסורתיות.
אזהרה לתעשייה
מתקפה זו ממחישה כיצד קמפיינים ממוקדים במיוחד נוטים להשתמש בטכניקות טכניות פשוטות כדי לעקוף מערכות הגנה אוטומטיות. ארגוני ייצור, גופים ממשלתיים ומגזרים תעשייתיים הקשורים לשרשראות אספקה אזוריות מהווים יעדים נפוצים, שכן התוקפים מצפים שהעובדים יעבירו ביניהם מסמכים וקבצים טכניים באופן שגרתי.
צוותי האבטחה בענפים אלה צריכים לנהוג בזהירות יתרה בכל הנוגע למסמכים המוגנים בסיסמה ולקבצים התומכים במאקרו. אפילו קבצים שנראים לגיטימיים, המועברים בדוא"ל, עלולים להסתיר טכניקות פריצה מתוחכמות שנועדו לעקוף את כלי הבדיקה המסורתיים.
למידע נוסף על מתקפה זו ולצפייה בניתוח המלא, בקרו בדו"חOPSWAT .
התקפה מס' 3: מסמך שנועד לגנוב פרטי הזדהות ומכוון לתשתיות קריטיות
הקשר
קמפיינים של ריגול סייבר מכוונים לעתים קרובות לארגונים הקשורים לממשל ולסביבות תשתית קריטיות. פעילות איומים הקשורה לאיראן התמקדה שוב ושוב בפריצות ממוקדות שנועדו לאסוף פרטי התחברות, מסמכים פנימיים ומידע מודיעיני מרשתות רגישות.
מדו"חות מודיעין האיומים עולה גם כי קמפיינים אלה נוטים לתת עדיפות לגניבת פרטי התחברות כנקודת אחיזה ראשונית. פרטי התחברות גנובים מאפשרים לתוקפים להרחיב את הגישה שלהם באופן בלתי מורגש ולשמור על נוכחות מתמשכת בסביבות המותקפות לאורך זמן.
סקירת ההתקפה
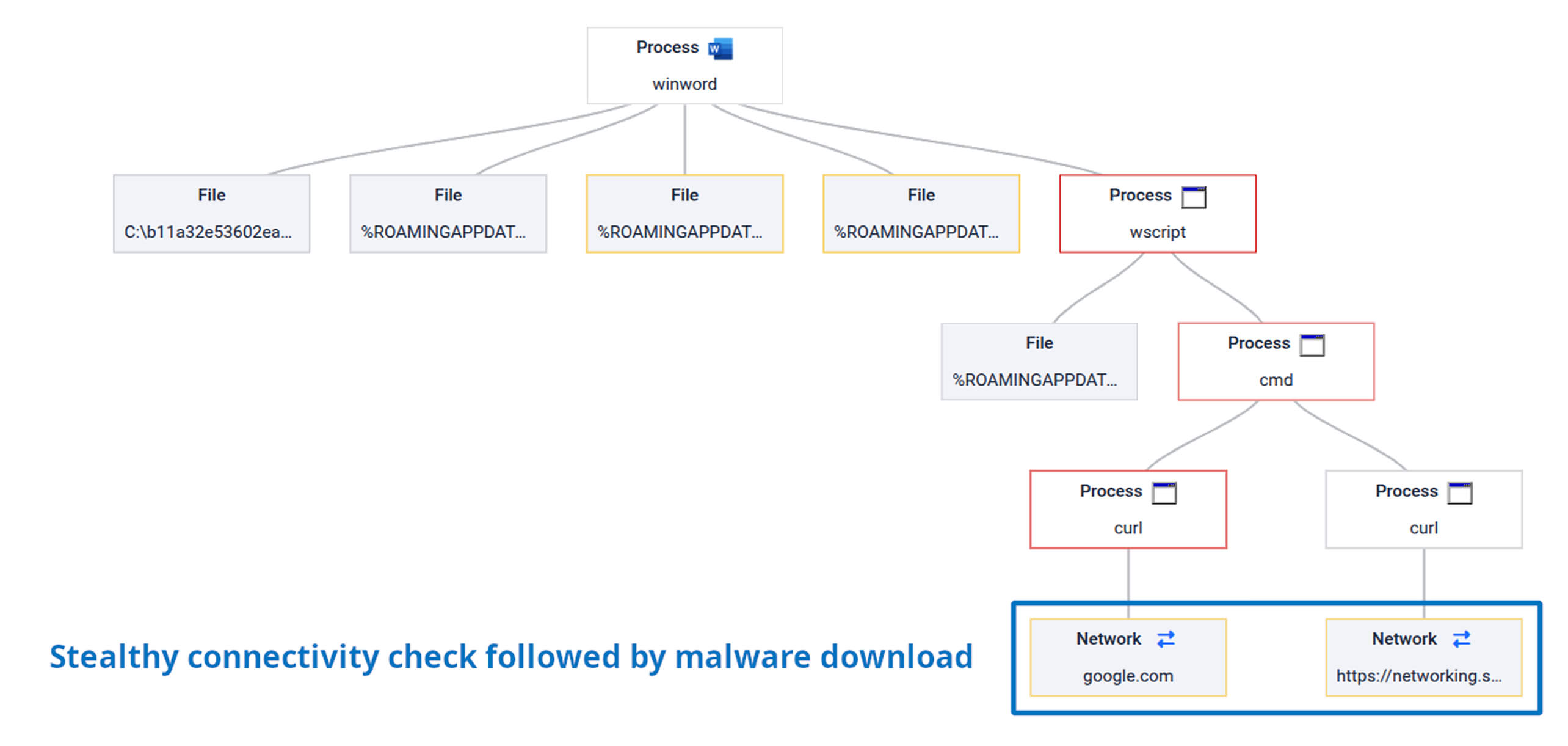
בדוגמה זו, התוקפים הפיצו מסמך Office זדוני שהכיל תוכן בשפה הפרסית, שנועד לפגוע בארגונים באיראן. המסמך נועד לאסוף מידע רגיש, כגון פרטי התחברות ומסמכים פנימיים, ובמקביל לצלם צילומי מסך מהמערכת הנגועה.
לאחר שהבטיחה את המשכיות פעולתה, התוכנה הזדונית ביצעה בדיקת קישוריות סמויה מול דומיין מהימן כגון google.com, לפני שהמשיכה בפעילותה. שלב זה נועד לוודא כי למערכת יש חיבור אינטרנט יציב, לפני תחילת תקשורת נוספת או גניבת נתונים פוטנציאלית.
אזהרה לתעשייה
דוגמה זו ממחישה כיצד איומים מסוג גניבת אישורים משמשים לעתים קרובות בפריצות ממוקדות לסביבות תשתית קריטיות. מגזרים אלה פועלים לרוב ברשתות מבוקרות, שבהן התוקפים נדרשים לאמת את הקישוריות לפני שהם מנסים לאסוף נתונים.
על ארגונים האחראים על מערכות קריטיות לעקוב מקרוב אחר התנהגות חשודה של מסמכים ובדיקות רשת בלתי צפויות המופעלות על ידי קבצים שנפתחו זה עתה. אינדיקטורים מוקדמים אלה עשויים להעיד על תחילתה של מתקפת פריצה נרחבת יותר.
למידע נוסף על מתקפה זו ולצפייה בניתוח המלא, בקרו בדו"חOPSWAT .
התקפה מס' 4: מסמך פישינג ממוקד של MuddyWater תחת הכותרת "הנחיות לאבטחת סייבר"
הקשר
MuddyWater היא קבוצת תקיפה שזכתה לפרסום נרחב, הקשורה לפעילות ריגול סייבר איראנית. חוקרים תיעדו כי הקבוצה פועלת נגד ארגונים דיפלומטיים, בתחום התקשורת, הפיננסי והממשלתי ברחבי המזרח התיכון, תוך שימוש בהודעות דוא"ל מסוג "ספיר-פישינג" ובמסמכים זדוניים.
דיווחים אחרונים מצביעים על כך שהקבוצה מפיצה שתל מבוסס Rust המכונה RustyWater באמצעות הודעות דוא"ל פישינג הכוללות מסמכי Word עם מאקרו, המוסווים כהנחיות לאבטחת סייבר. הקמפיין מכוון לארגונים ברחבי המזרח התיכון ומסתמך על פיתיונות משכנעים כדי לגרום להפעלת המאקרו.
סקירת ההתקפה
בדוגמה זו, התוקפים שלחו דוא"ל פישינג ממוקד שכותרתו "הנחיות אבטחת סייבר" מחשבון לגיטימי הקשור mobile אזורי. הדוא"ל הכיל מסמך Word זדוני שנועד להיראות כמו נוהל שגרתי או הודעת אבטחה.
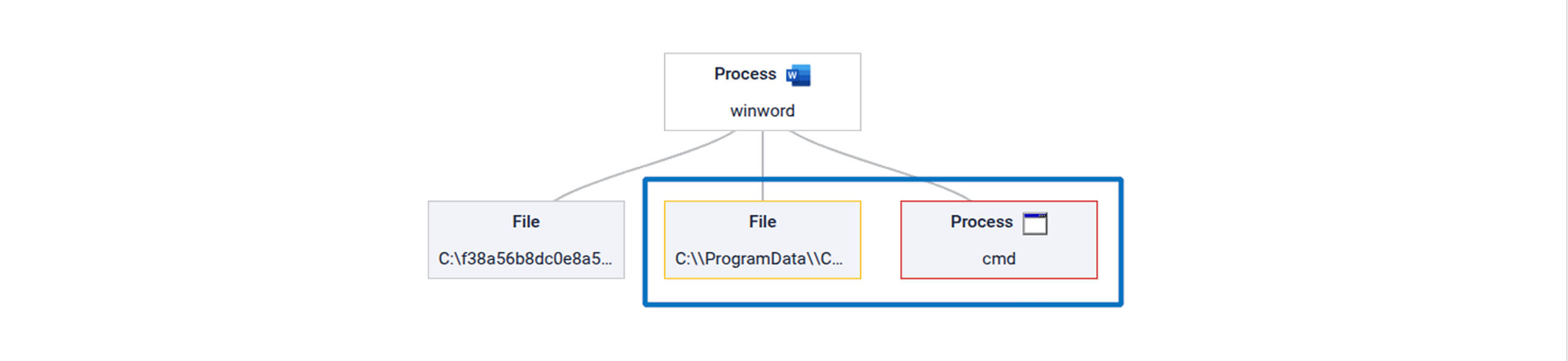
לאחר שהמאקרו הושפע, המסמך חילץ מטען מקודד בשיטת הקסדצימלית שהוטמע בתוך הקובץ, ושחזר אותו לקובץ הפעלה של Windows. התוכנה הזדונית נכתבה לדיסק והופעלה באמצעות לוגיקה מוסתרת, שבמהלך ההפעלה בנתה מחדש מחרוזות מפתח כדי להקשות על ניתוח המאקרו.
הקובץ ההפעלה שהופץ הטמיע שתל מבוסס Rust, שכלל מנגנוני הגנה מפני איתור באגים, מחרוזות פעולה מוצפנות ובדיקות של כלי אבטחה מותקנים, לפני שהקים תקשורת פיקוד ושליטה.
אזהרה לתעשייה
מתקפה זו ממחישה כיצד קמפיינים ממוקדים של פישינג מסתמכים לעתים קרובות על נושאים מציאותיים הקשורים למדיניות או לאבטחה, כדי להגדיל את הסיכוי שהנמענים יפתחו את הקבצים המצורפים. ארגונים דיפלומטיים, ספקי תקשורת ומוסדות פיננסיים נותרים יעד תדיר לקמפיינים אלה.
צוותי האבטחה במגזרים אלה צריכים לנהוג בזהירות במסמכים הכוללים פונקציות מאקרו, במיוחד כאשר הם נשלחים באמצעות הודעות דוא"ל בלתי צפויות. אפילו קבצים שנראים כמכילים הנחיות שגרתיות בנושא אבטחת סייבר עלולים להסתיר תוכנות זדוניות שנועדו ליצור גישה לפריצה לטווח ארוך.
למידע נוסף על מתקפה זו ולצפייה בניתוח המלא, בקרו בדו"חOPSWAT .
התקפה מס' 5: תוכנת הזדון "CraftyCamel Polyglot" המכוונת לתעשיית התעופה והתחבורה
הקשר
מספר הקמפיינים הממוקדים מאוד נגד ארגוני תעופה ותחבורה הלך וגבר, שכן התוקפים מחפשים דרכים להשיג גישה לסביבות תפעוליות רגישות. מגזרים אלה מנהלים לעתים קרובות מערכות ושרשראות אספקה מורכבות, מה שהופך אותם ליעדים אטרקטיביים לריגול ולפריצות לטווח ארוך.
בדיווחים אחרונים מתוארת מתקפה המכונה CraftyCamel, שהשתמשה בקבצים רב-לשוניים המסוגלים לתפקד במספר פורמטים בו-זמנית. קבצים אלה תוכננו לעקוף כלי בדיקה מסורתיים, תוך שהם מכוונים לסביבות תעופה וטכנולוגיה תפעולית.
סקירת ההתקפה
בדוגמה זו, התוקפים שלחו דוא"ל פישינג שתוכנן בקפידה, שנשלח מחברה לגיטימית שנפרצה כדי להגביר את האמינות. ההודעה כללה ארכיון ZIP שהכיל קבצים שהוסוו כמסמכים לגיטימיים, אך נועדו להפעיל קוד נסתר.
בתוך הארכיון השתמשו התוקפים בקבצים רב-לשוניים, בהם מסמך Excel מזויף שהיה למעשה קיצור דרך של Windows (LNK) ושילובים נוספים של קבצי PDF/HTA ו-PDF/ZIP. קבצים אלה ניצלו לרעה כלי עזר מהימנים של Windows, כגון mshta.exe, כדי להריץ סקריפטים מוסתרים ובסופו של דבר לטעון את מטען התוכנה הזדונית הסופי, שהוסווה כתמונה.
אזהרה לתעשייה
התקפה זו ממחישה כיצד קמפיינים מודרניים לפריצה מסתמכים יותר ויותר על מבני קבצים מורכבים כדי לחמוק מכלי זיהוי מסורתיים. ארגונים בתחומי התעופה, הלוויינים, התקשורת והתחבורה נמצאים בסיכון גבוה במיוחד, שכן הם מחליפים באופן קבוע מסמכים טכניים וקבצים תפעוליים.
צוותי האבטחה בענפים אלה צריכים להיות מודעים לכך שקבצים הנראים כמסמכים תמימים עלולים להסתיר פורמטים משולבים רבים או נתיבי הפעלה נסתרים. זיהוי איומים אלה מחייב בדיקה מעמיקה המסוגלת לחשוף התנהגות זדונית המסתתרת בתוך מבני קבצים מורכבים.
למידע נוסף על מתקפה זו ולצפייה בניתוח המלא, בקרו בדו"חOPSWAT .
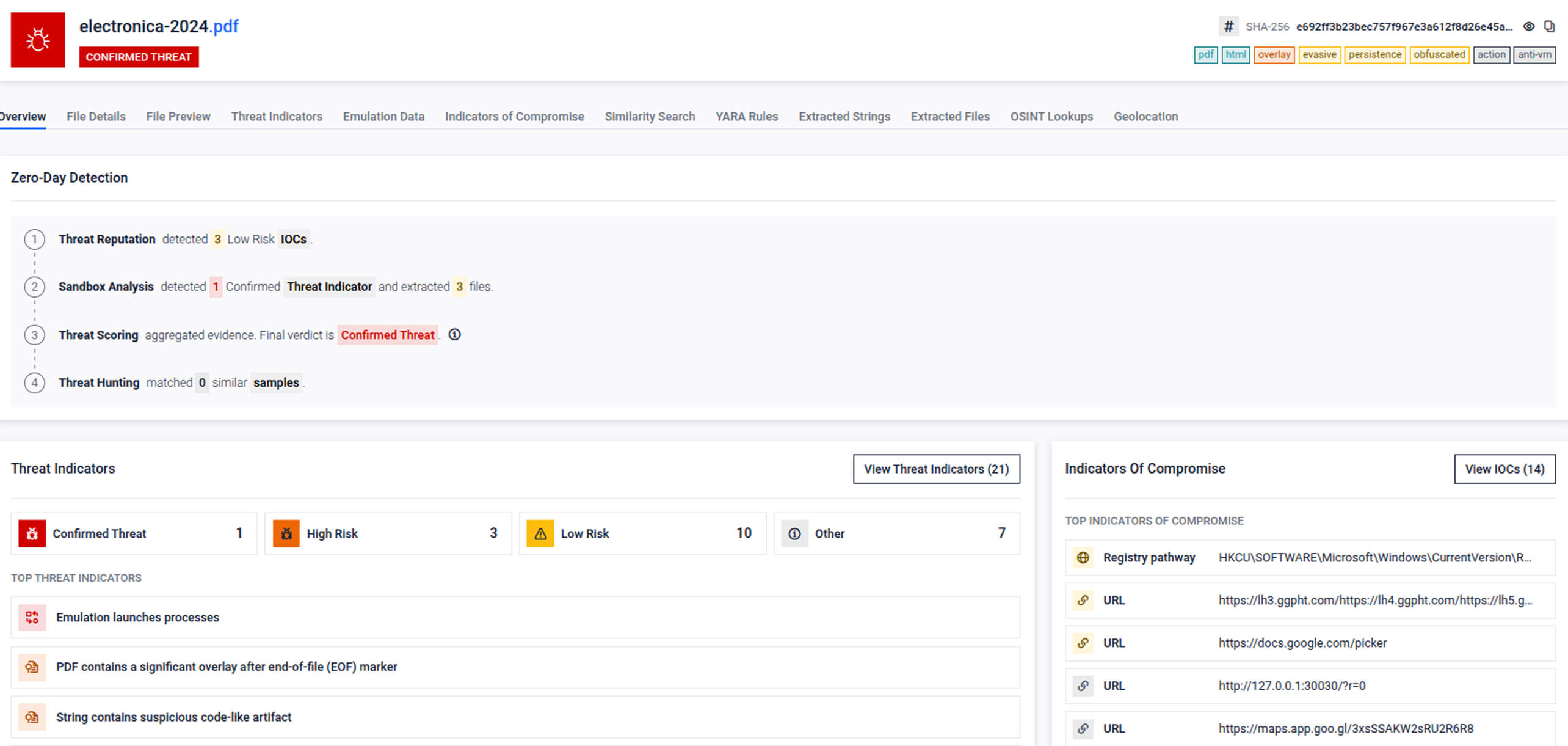
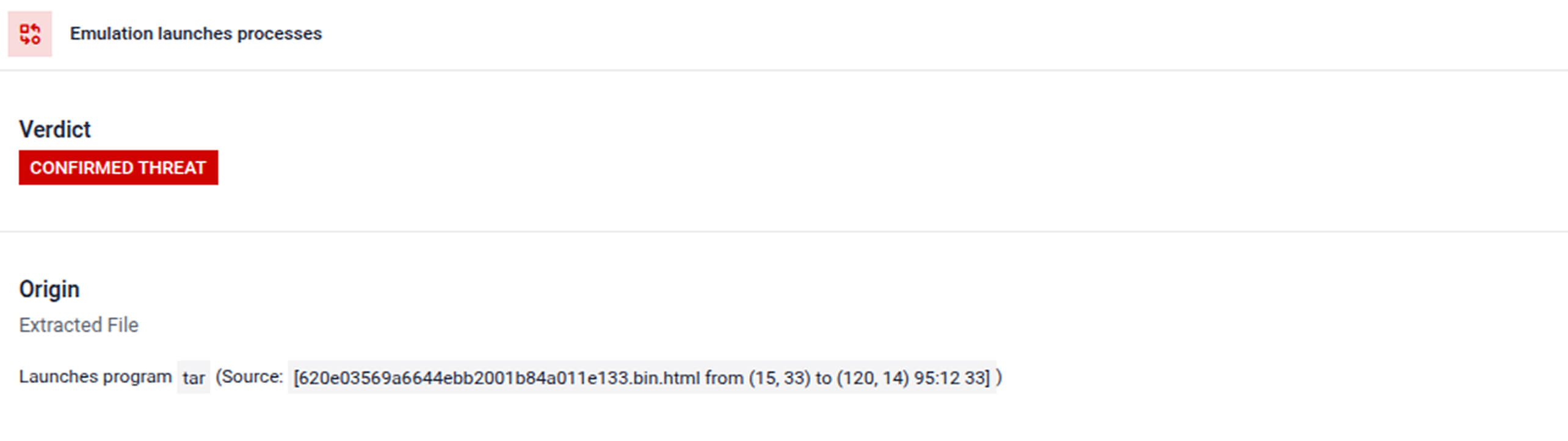
כיצד זיהתה MetaDefender את כל החמש
דוגמאות אלה ממחישות דפוס נפוץ: התוקפים מסתמכים על קבצים שנוצרו בקפידה במטרה לעקוף את הבדיקות המסורתיות. מסמכים עם מאקרו, סקריפטים מוגנים וקבצים רב-לשוניים נועדו כולם לעקוף סריקה מבוססת חתימות וניתוח סטטי בסיסי.
MetaDefender מתמודדת עם אתגר זה באמצעות מערך זיהוי אחיד של תקיפות "יום אפס", המנתח כל קובץ באמצעות מספר שכבות משלימות. במקום להסתמך על טכניקת זיהוי אחת בלבד, המערכת מעריכה את המוניטין, ההתנהגות וסימני הדמיון כדי להציג לצוותי האבטחה תוצאה אחת מהימנה.
הצינור משלב ארבע שכבות הפועלות יחד:
- בדיקות מוניטין איומים מול מאגר מודיעין עולמי המכיל מיליארדי אינדיקטורים
- סביבת בדיקה אדפטיבית ברמת ההוראות, המד מה את התנהגות המעבד ומערכת ההפעלה כדי לחשוף פעילות זדונית במהלך הביצוע
- דירוג איומים המשלב אינדיקטורים התנהגותיים, נתוני מוניטין ותוצאות ניתוח לכדי הערכת סיכונים אחידה
- "ציד איומים" עושה שימוש בחיפוש דמיון מבוסס למידת מכונה, המזהה גרסאות תוכנות זדוניות קשורות ודפוסים של קמפיינים
יחד, שכבות אלה חושפות התנהגויות מתחמקות כגון הפעלת מאקרו נסתרת, העברת מטען בשלבים וטכניקות למניעת ניתוח. התוצאה היא קביעה אחת ברורה וניתנת ליישום לכל קובץ, המאפשרת לצוותי האבטחה לזהות התקפות ממוקדות במהירות, תוך צמצום "רעשי הרקע" בחקירה.
מה שמראים המקרים הללו
חמש הדוגמאות הללו ממחישות כיצד מתקפות APT מודרניות מתוכננות לעקוף אמצעי אבטחה מסורתיים. כל קמפיין הסתמך על טכניקות כגון מסמכי פישינג ממוקד, פקודות מאקרו מוגנות, העברת מטען זדוני בשלבים או קבצים רב-לשוניים, כדי להסתיר פעילות זדונית בתוך קבצים שנראים שגרתיים.
בסיכום, מקרים אלה מראים כי MetaDefender מסוגל לזהות באופן עקבי איומים ספציפיים לאזור, דפוסי תקיפה המותאמים לתחומים עסקיים שונים ותוכנות זדוניות המתחמקות מזיהוי, במגוון רחב של תרחישי פריצה:
1. מתקפות ממוקדות מסתמכות במידה רבה על טכניקות פריצה המבוססות על קבצים.
מסמכי פישינג ממוקד, קבצים מצורפים מוסווים ומבני קבצים מורכבים נותרים נקודות כניסה נפוצות לסביבות רגישות.
2. תוקפים מפתחים יותר ויותר תוכנות זדוניות שנועדו לעקוף ניתוחים אוטומטיים.
טכניקות כגון מאקרו מוגנים, העברת מטען בשלבים ובדיקות נגד ניתוח נועדו לעקוף את כלי הבדיקה המסורתיים.
3. הזיהוי חייב להישאר עקבי בכל טכניקות התקיפה השונות.
צוותי האבטחה אינם יכולים להסתמך על שיטת זיהוי אחת בלבד כאשר קמפיינים עושים שימוש במגוון פורמטים של קבצים ואסטרטגיות הפצה.
4. בדיקה התנהגותית היא חיונית לזיהוי איומים סמויים.
התבוננות באופן שבו קובץ מתנהג במהלך ההפעלה עשויה לחשוף פעילות זדונית שהבדיקה הסטטית לבדה עלולה להחמיץ.
באמצעות שילוב של נתוני מוניטין, ניתוח התנהגות, דירוג איומים וזיהוי דמיון, MetaDefender מספקת זיהוי עקבי וניתן לשחזור גם כאשר התוקפים מסווים את הכלים, המטענים או שיטות ההפצה שלהם. והחשוב ביותר, מקרים אלה מראים כי ניתן לזהות קמפיינים ממוקדים שנועדו לעקוף את מערכות ההגנה המסורתיות עוד בטרם הם משיגים את מטרתם.
מדוע זה חשוב בסביבות מפוקחות ובסביבות בעלות סיכון גבוה
התקפות APT ממוקדות כמעט אף פעם אינן מכוונות לקורבנות אקראיים. הן מתמקדות בארגונים שבהם גניבת מידע, שיבוש פעילות או גישה לטווח ארוך עשויים להקנות יתרון אסטרטגי.
גופים ממשלתיים, ארגוני ביטחון, מוסדות פיננסיים ויצרנים מתמודדים עם בעיה משותפת: איומים ממוקדים המבוססים על קבצים, שנועדו לעקוף את הבדיקות המסורתיות. סביבות אלה תלויות בהחלפת מסמכים מאובטחת, בעדכוני תוכנה ובהמשכיות תפעולית, מה שהופך קובץ זדוני בודד לנקודת חדירה בעלת השלכות חמורות.
MetaDefender תומך בדרישות אלה באמצעות זיהוי מאוחד של איומים מסוג "יום אפס", המיועד לסביבות המפוקחות ובעלות סיכון גבוה. מערך הזיהוי של המערכת מספק מודיעין קונטקסטואלי, נראות ברמה פורנזית, דיווח מונחה תאימות, וכן קביעה אחת מהימנה לכל קובץ. הדבר מסייע לארגונים לקיים איתור איומים יזום, תוך שמירה על תאימות למסגרות כגון NERC CIP, NIS2, IEC 62443, SWIFT CSP ו-CMMC.
ארגונים הפועלים במגזרים אלה אינם יכולים להניח שתקיפות מתוחכמות יפסיקו להתפתח. אך באמצעות שילוב של בדיקת התנהגות עם ניתוח מבוסס מודיעין, צוותי האבטחה יכולים לחשוף איומים ממוקדים בטרם יפגעו במערכות קריטיות.
גלו דוגמאות אמיתיות של APT שזוהו על ידי MetaDefender .
קראו עוד על MetaDefender ועל זיהוי מאוחד של תקיפות "יום אפס".